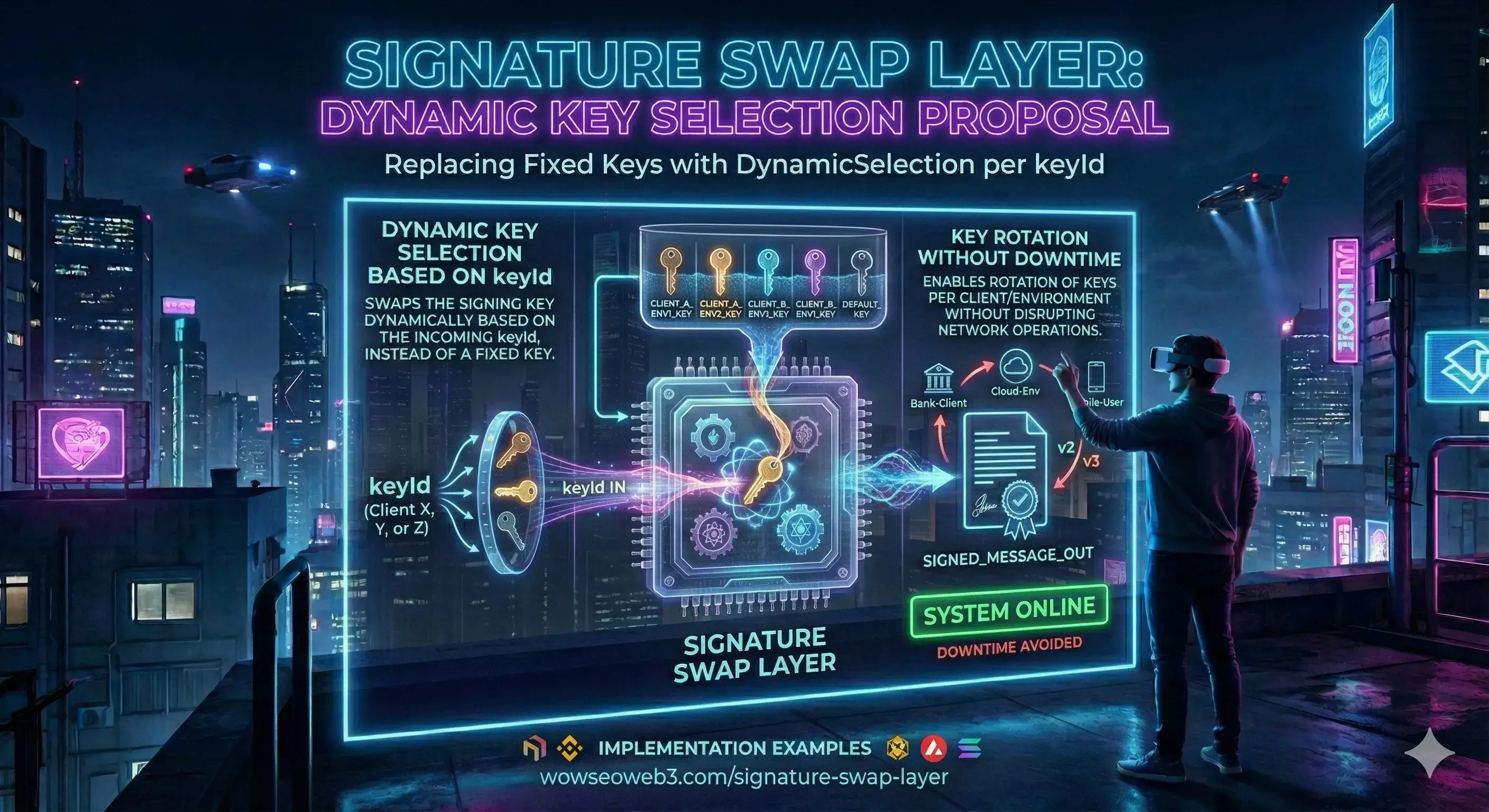
Signature Swap Layer: Dynamic Key Selection by keyId in Z-GAP
Zero-downtime key rotation and canonical request signing for production Web3 APIs
Executive Summary
In traditional API security, every service shares one global secret. When that secret is compromised, the only remedy is an emergency redeploy—taking the entire system offline while you rotate credentials.
The Signature Swap Layer eliminates this single point of failure. Inside the Z-GAP guard, every incoming request carries a keyId header. The guard dynamically selects the matching secret from a versioned key store, verifies the HMAC-SHA256 signature, and proceeds—all in microseconds.
This article explores the key management challenge in Web3 APIs, walks through the signature swap flow step by step, details the canonical signing process, and explains the operational benefits of keyId-based secret isolation.
Part 1: The Key Management Challenge
When your Web3 platform grows beyond a single service, key management becomes a critical attack surface. The WSEO ecosystem connects multiple clients—the wow4 frontend on Netlify, the core-engine on Railway, and external partners like SolidityScan—each needing authenticated access to protected endpoints.
With a single shared secret, a compromise in any of these systems exposes all of them. Worse, rotating that secret requires synchronized deployments across every client simultaneously—a logistical nightmare that often leads teams to delay rotation for months.
Single Key Risk
One compromised key exposes every service. There's no isolation between clients, environments, or deployment stages.
Synchronized Deploys
Rotating a global secret requires every client to update simultaneously—or face authentication failures during the transition window.
No Audit Trail
With a single key, you cannot distinguish which client made a request. Forensic analysis after a breach becomes impossible.
Part 2: How the Signature Swap Layer Works
The "swap" in Signature Swap Layer refers to the dynamic selection of signing secrets at runtime. Instead of one hardcoded key, the Z-GAP guard maintains a versioned key store where each entry has a unique client identifier.
The Signature Swap Flow
Client sends keyId header
The request includes a signed header identifying which secret was used to sign. The wow4 frontend, the core-engine internal scripts, and external partners each have their own unique key identifier.
Guard resolves the matching secret
The Z-GAP middleware reads the secure key store and finds the entry matching the provided key identifier. If no match is found, the request is immediately rejected with 401 Unauthorized.
Canonical string is rebuilt
The guard reconstructs the canonical string from the incoming request—including method, path, timestamp, nonce, and payload hash—exactly the same way the client built it before signing.
HMAC-SHA256 verified in constant time
The expected HMAC is computed with the resolved secret and compared using a constant-time comparison function. This prevents timing side-channel attacks that could leak information about the secret's value.
Related: Z-GAP Full Architecture
The Signature Swap Layer is one component of the Z-GAP toolkit. Read the full overview covering anti-replay, rate limiting, and payload integrity.
Read the Z-GAP Rollout article →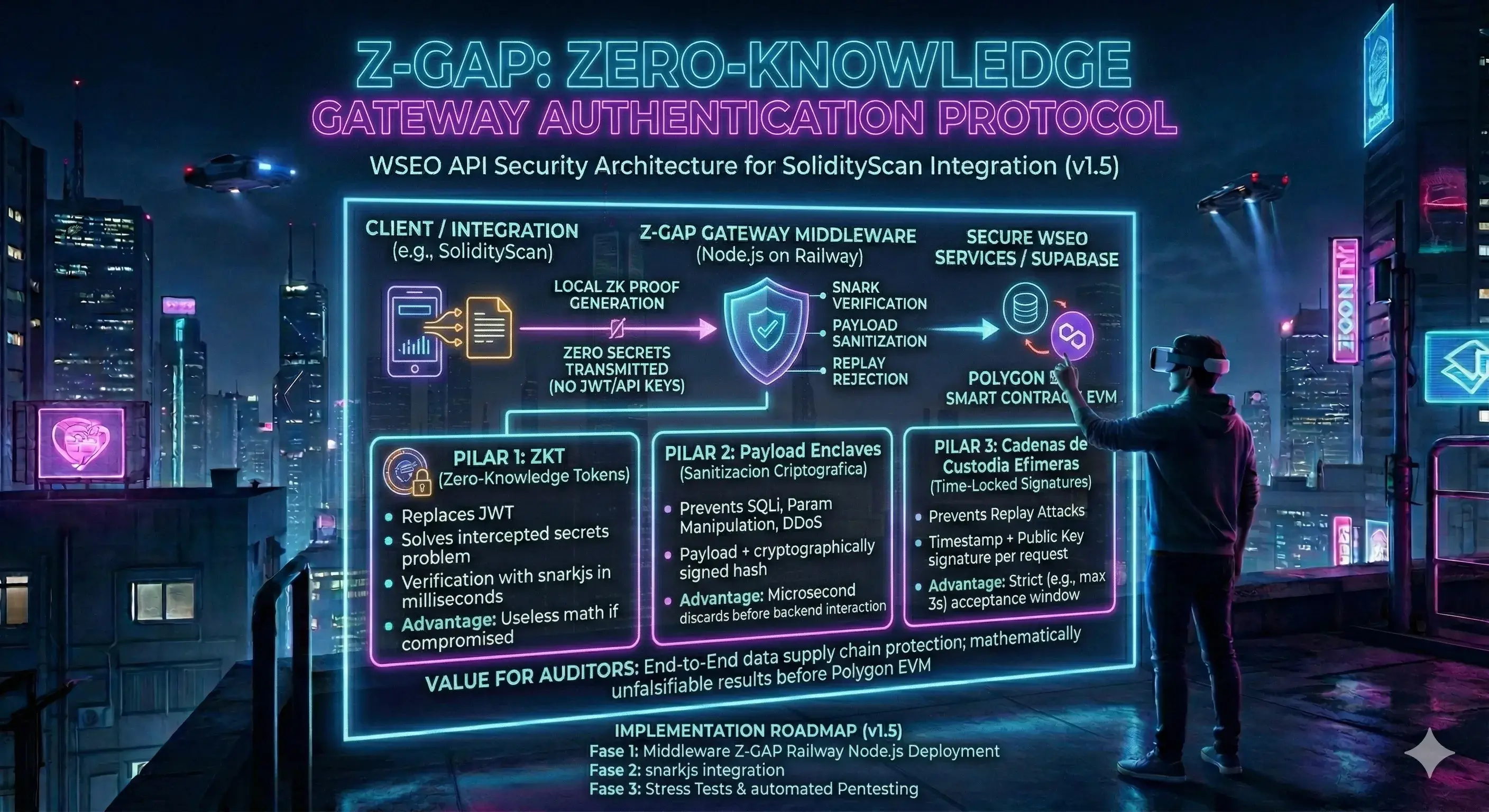
Part 3: Canonical Signing In Detail
Both the client and the server must produce the exact same canonical string for the signature to verify. Any deviation—even a trailing slash or different casing—causes a mismatch. This is intentional: it guarantees that the signed request is bit-for-bit identical on both ends.
Construct the Canonical String
Concatenate the HTTP method (uppercase), the request path (normalized), the current Unix timestamp, a unique nonce, and the SHA-256 hash of the canonicalized request body. These components form a deterministic string that both client and server reproduce independently.
Compute HMAC-SHA256
Using the secret associated with your key identifier, compute the HMAC-SHA256 of the canonical string. The result is hex-encoded and sent as the signature header alongside the request.
Attach All Z-GAP Headers
The signed request includes five custom headers: the client key identifier, timestamp, nonce, payload hash, and cryptographic signature. The server uses these to independently reconstruct and verify the signature.
On the client side, this entire process is handled by a compact helper function that abstracts all the cryptographic details. Frontend developers don't need to understand cryptography—they just call the helper before each API request.
Part 4: Operational Benefits
- Zero-downtime rotation: Add a new key entry to the secure key store, distribute it to the target client, and deprecate the old key—all while traffic continues flowing through existing keys.
- Per-client isolation: Each service (frontend, backend, SolidityScan) has its own keyId. A breach in one client does not compromise the others. You can revoke a single key without affecting the rest of the ecosystem.
- Forensic auditability: Since every request carries its keyId, server logs can trace exactly which client made each call—critical for post-incident investigation.
- Environment segmentation: Use different keyIds for staging, production, and CI/CD pipelines. A staging key can never authenticate against production endpoints.
- No emergency redeploys: When a key is compromised, phase it out by keyId policy. The old key is removed from the store; the attacker's captured signatures immediately become invalid.
Conclusion: Dynamic Keys for a Dynamic Ecosystem
In Web3, where reputation data flows through multiple services before becoming immutable on-chain, the security of each intermediate step matters as much as the smart contract itself. The Signature Swap Layer ensures that every link in this chain is independently authenticated, auditable, and rotatable without disruption.
Frequently Asked Questions
What is the Signature Swap Layer?
The Signature Swap Layer is the dynamic key selection mechanism inside the Z-GAP guard. Instead of using a single hardcoded secret for all API clients, it resolves the correct signing key at runtime based on the client’s key identifier — enabling per-client isolation and zero-downtime key rotation.
How is the keyId sent?
The client includes a custom HTTP header with every signed request that identifies which secret was used. The Z-GAP guard uses this value to look up the corresponding secret in the secure key store. If the identifier is not found, the request is rejected immediately.
Can multiple keys be active simultaneously?
Yes. The secure key store supports multiple entries at once. This is the core feature that enables zero-downtime rotation: you add the new key, distribute it to the target client, verify it works, and then remove the old key from the store.
What happens if a key is compromised?
Remove the compromised key identifier from the secure key store. All requests signed with that key are immediately rejected. Other clients using different key identifiers are completely unaffected—no emergency redeploy, no synchronized rotation, no downtime.
Rate this Article
Help us improve the Signature Swap Layer documentation.
4.9/5 based on community votesStay Ahead of Web3 Security
Subscribe to receive the latest Z-GAP updates, security advisories, and WSEO protocol news directly to your inbox.
No spam. Unsubscribe at any time.
WowSeoWeb3
Web3 Security & Visibility Protocol
Pioneering the standard for decentralized reputation. We help projects verify their integrity and provide investors with verified due diligence.