Z-GAP Operational Rollout: Unified Gateway Security Toolkit
How Zero-Knowledge Gateway Authentication Protocol protects every API request in the WSEO ecosystem
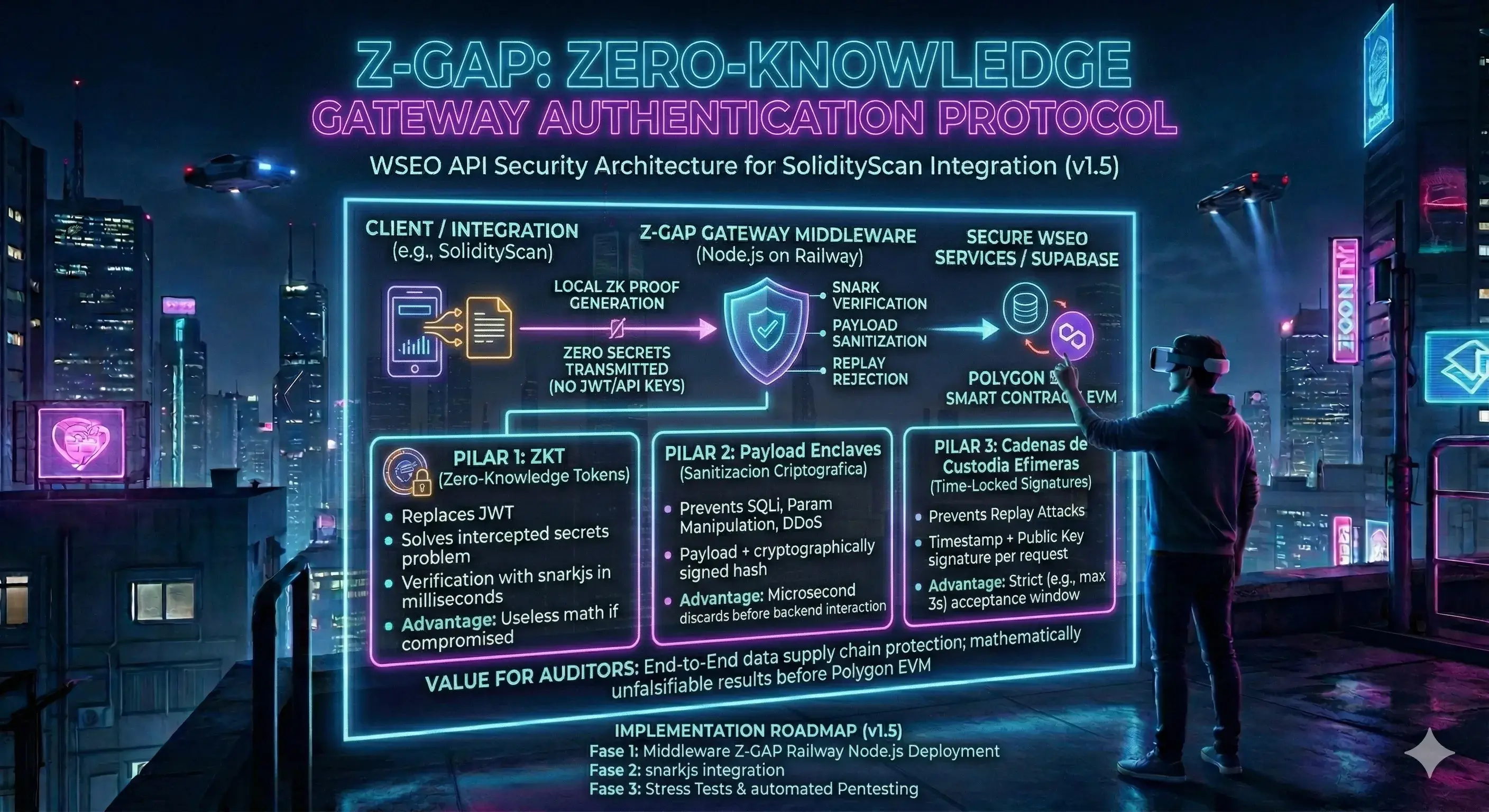
Executive Summary
99% of Web3 APIs rely on static API keys or JWTs. If a hacker intercepts a single HTTP request or gains access to the server, they can steal credentials and forge reputation scores. This is the "silent threat" that almost no Web3 project addresses.
Z-GAP (Zero-Knowledge Gateway Authentication Protocol) is our answer. It is not just a middleware—it is a unified security toolkit that intercepts every protected request and validates it cryptographically before any business logic runs.
This article explains the API security gap in Web3, details the three pillars of Z-GAP architecture, walks through each unified control currently active in production, and provides the operational rollout checklist for self-hosting teams.
Part 1: The API Security Gap in Web3
Most Web3 protocols invest heavily in smart contract audits—and rightfully so. But the off-chain layer that feeds data to those contracts is often protected by nothing more than a static API key stored in an environment variable.
Consider what happens when an attacker intercepts a legitimate API call between your frontend and your scoring engine. With a traditional setup, they can replay the same request seconds later, tamper with the payload to change a project's reputation score, or flood the endpoint to exhaust resources.
Replay Attacks
An attacker captures a valid signed request and sends it again minutes later. Without timestamp windows and nonce tracking, the server happily re-executes the same operation—potentially minting duplicate SBTs or overwriting scores.
Payload Tampering
Man-in-the-middle attacks can modify the JSON body between client and server. Without cryptographic body hashing, a score of 85 can silently become 25—or vice versa—before reaching your database.
Static Key Compromise
A single leaked API key grants permanent access. There's no built-in expiration, no per-client isolation, and no way to rotate credentials without a full redeploy. In Web3, where reputation data becomes immutable on-chain, a single breach can have permanent consequences.
Part 2: The Z-GAP Architecture
Z-GAP extends the Zero-Knowledge philosophy from the blockchain layer to the API orchestration layer. No signing material travels over the network. Instead, each request carries a mathematical proof of authenticity that the server verifies independently.
Related: Signature Swap Layer
Dive deeper into how Z-GAP dynamically selects signing keys per client and environment—enabling zero-downtime key rotation.
Read the Signature Swap Layer article →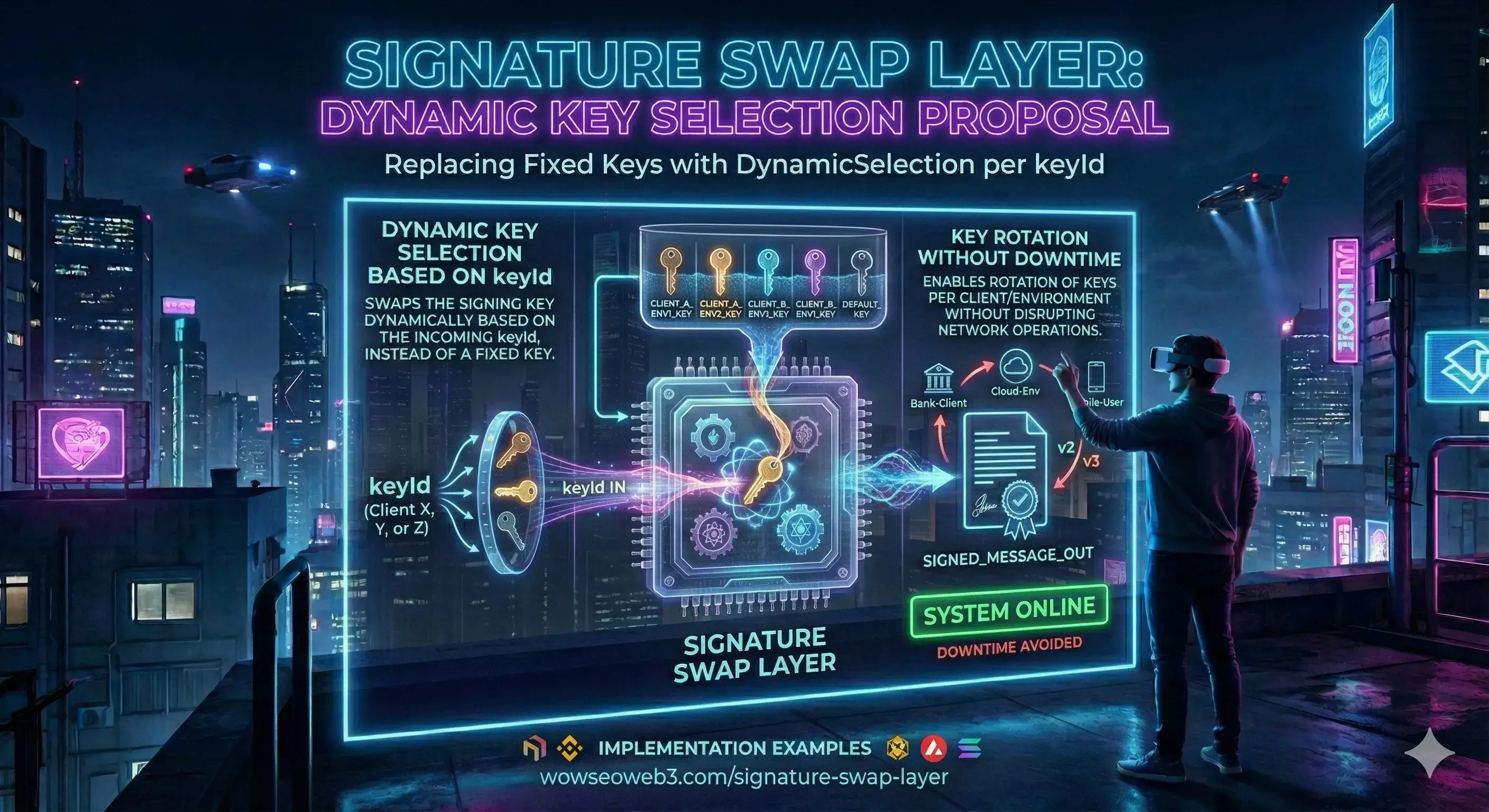
The Three Pillars of Z-GAP
1. Signed Identity (Replaces JWT)
Instead of a traditional token containing readable data, the client generates an HMAC-SHA256 signature from a canonical string that includes the HTTP method, path, timestamp, a unique nonce, and a hash of the payload. The server independently reconstructs the same string and verifies the signature in constant time. No signing material ever travels over the wire.
2. Payload Enclaves (Cryptographic Sanitization)
Before your business logic reads a single byte of the request body, the Z-GAP middleware demands a signed payload hash. The body is canonicalized, hashed with SHA-256, and compared against the hash included in the signed headers. Any tampering—even a single character—triggers immediate rejection.
3. Ephemeral Custody Chains (Time-Locked Signatures)
Each request is signed with the current timestamp. The server only accepts requests within a strict time window. Combined with unique nonce tracking per client and endpoint, this eliminates replay attacks completely—even if an attacker captures a valid request off the wire.
Part 3: Unified Controls in Production
Z-GAP runs as a global pre-handler hook in the WSEO Core Engine. Before any scoring, scraping, or QEP logic executes, every request to protected routes passes through the following checks:
Signature Verification
Five signed headers—client identity, timestamp, nonce, payload hash, and cryptographic signature—are validated for presence and format. The canonical string is reconstructed server-side and HMAC-SHA256 is verified in constant time.
Payload Integrity
The request body is canonicalized and hashed. If the computed hash doesn't match the signed payload hash header, the request is rejected with 401 before it reaches any business logic.
Anti-Replay Defense
Each nonce-timestamp combination is tracked per client identity and endpoint. Duplicate requests return 409 Conflict. Expired timestamps return 401. This prevents both immediate replays and delayed attack windows.
Rate Limiting & Runtime Policy
Per-key throttling windows prevent DDoS-style abuse. Protected paths are managed through a runtime configuration layer that can be updated without code changes. Rejection rates (401, 409, 429) are monitored for anomaly detection.
Part 4: Operational Rollout & Best Practices
Z-GAP was designed for zero-risk progressive activation. You don't have to enable everything at once.
- Step 1 — Deploy inactive: Deploy the middleware in observation mode. It loads but does not enforce. Zero risk of breaking existing flows.
- Step 2 — Generate keys: Use the key generation script to create versioned secrets in the secure key store. Each key has a unique identifier for per-client isolation.
- Step 3 — Activate per-endpoint: Enable on a single protected route first. Validate end-to-end calls. Then progressively add more routes.
- Step 4 — Monitor rejections: Track
401,409, and429rejection rates. Spikes indicate either misconfigured clients or active attack attempts. - Step 5 — Rotate keys: Use the Signature Swap Layer (keyId-based selection) to phase out compromised or old keys without downtime.
Conclusion: Security Is Not Optional
In Web3, reputation data becomes immutable once it's anchored on-chain. A single forged score or tampered payload can permanently damage the credibility of the entire ecosystem. Z-GAP ensures that the data pipeline feeding the blockchain is as trustless and verifiable as the blockchain itself.
Ready to see your project's security posture?
- Analyze your project at wowseoweb3.com/wseo.
- Review the Z-GAP rollout checklist above.
- Certify your reputation on-chain via SEOBeacon.
Frequently Asked Questions
What is Z-GAP?
Z-GAP (Zero-Knowledge Gateway Authentication Protocol) is a unified security middleware that protects API endpoints by validating cryptographic signatures, enforcing anti-replay policies, checking payload integrity, and applying rate limits—all before any business logic runs. It extends the Zero-Knowledge philosophy from on-chain to the API orchestration layer.
Why not just use API keys or JWTs?
Static API keys and JWTs contain readable credentials that travel over the network. If intercepted, they grant full access with no expiration mechanism. Z-GAP uses HMAC-SHA256 signatures—the signing material never leaves the server or client. Even if an attacker captures a request, the signature is bound to a specific timestamp, nonce, and payload hash, making it useless for replay.
How does key rotation work?
Z-GAP selects the signing material dynamically using a key identifier sent with each request. Multiple keys can coexist in the secure key store, allowing you to issue new keys to specific clients or environments while phasing out old ones—all with zero downtime.
Does Z-GAP slow down my API?
No. HMAC-SHA256 verification completes in microseconds. In fact, Z-GAP improves performance by rejecting invalid requests before they reach your database or scoring engine. Abusive traffic is filtered at the gateway level, protecting expensive downstream operations.
Rate this Article
Help us improve the Z-GAP security documentation.
4.8/5 based on community votesStay Ahead of Web3 Security
Subscribe to receive the latest Z-GAP updates, security advisories, and WSEO protocol news directly to your inbox.
No spam. Unsubscribe at any time.
WowSeoWeb3
Web3 Security & Visibility Protocol
Pioneering the standard for decentralized reputation. We help projects verify their integrity and provide investors with verified due diligence.